Widespread use of smart phones by employees to perform work related activities has introduced the idea of using these devices as an authentication token. As an example of such attempts, RSA SecureID software tokens are available for iPhone, Nokia and the Windows platforms. Obviously, mobile phones would not be able to provide the level of tamper-resistance that hardware tokens would, but I was interested to know how easy/hard it could be for a potential attacker to clone RSA SecureID software tokens. I used the Windows version of the RSA SecurID Software Token for Microsoft Windows version 4.10 for my analysis and discovered the following issues:
Device serial number of tokens can be calculated by a remote attacker :
Every instance of the installed SecurID software token application contains a hard drive plug-in (implemented in tokenstoreplugin.dll) that has a unique device serial number. This serial number can be used for “Device Binding” and the RSA documentation defines it as follows:
“Before the software token is issued by RSA Authentication Manager, an additional extension attribute (<DeviceSerialNumber/>) can be added to the software token record to bind the software token to a specific devicedevice serial number is used to bind a token to a specific device. If the same user installs the application on a different computer, the user cannot import software tokens into the application because the hard drive plug-in on the second computer has a different device serial number from the one to which the user’s tokens are bound”.
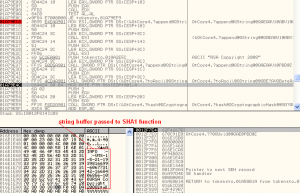
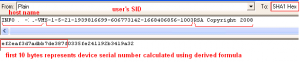
Reverse engineering the Hard-Disk plugin (tokenstoreplugin.dll) indicated that the device serial number is dependent on the system’s host name and current user’s windows security identifier (SID). An attacker, with access to these values, can easily calculate the target token’s device serial number and bypass the above mentioned protection. Account SIDs can be enumerated in most of the Microsoft active directory based networks using publicly available tools, if the “enumeration of SAM accounts and shares” security setting was not set to disabled. Host names can be easily resolved using internal DNS or Microsoft RPC. The following figures show the device serial number generation code:
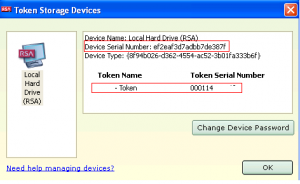 The SecureID device serial number calculation can be represented with the following formula:
The SecureID device serial number calculation can be represented with the following formula:
device_serial_number=Left(SHA1(host_name+user_SID+“RSA Copyright 2008”),10)
Token’s copy protection:
The software token information, including the secret seed value, is stored in a SQLite version 3 database file named RSASecurIDStorage under the “%USERPROFILE%\Local Settings\Application Data\RSA\RSA SecurID Software Token Library” directory. This file can be viewed by any SQLite database browser, but sensitive information such as the checksum and seed values are encrypted. RSA documentation states that this database file is both encrypted and copy protected: “RSA SecurID Software Token for Windows uses the following data protection mechanisms to tie the token database to a specific computer:
• Binding the database to the computer’s primary hard disk drive
• Implementing the Windows Data Protection API (DPAPI)
These mechanisms ensure that an intruder cannot move the token database to another computer and access the tokens. Even if you disable copy protection, the database is still protected by DPAPI.”
The RSASecurIDStorage database file has two tables: PROPERTIES and TOKENS. The DatabaseKey and CryptoChecksum rows found in the PROPERTIES tables were found to be used for copy protection purpose as shown in the figure below:
Reverse engineering of the copy protection mechanism indicated that:
- The CryptoChecksum value is encrypted using the machine’s master key, which can only be decrypted on the same computer system, unless the attacker can find a way to import the machine key and other supporting data to their machine
- The DatabaseKey is encrypted using the current logged-on user’s master key and provides token binding to that user account
Previous research on the Microsoft Windows DPAPI internals has made offline decryption of the DPAPI protected data possible. This means that if the attacker was able to copy the RSA token database file along with the encryption master keys to their system (for instance by infecting a victim’s machine with a rootkit), then it would be possible to decrypt the token database file on their machine. The detailed attack steps to clone a SecurID software token by copying the token database file from a victim’s system are as follows:
- Copy the token database file, RSASecurIDStorage, from the user profile directory
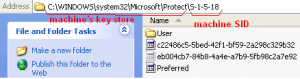
- Copy the user’s master key from %PROFILEDIR%\Application Data\Microsoft\Protect\%SID%; the current master key’s GUID can be read from Preferred file as shown in the figure below:
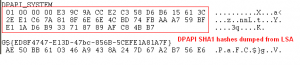
- Copy the machine’s master key from the %WINDIR%\system32\Microsoft\Protect\ directory. Microsoft Windows protects machine keys against tampering by using SHA1 hash values, which are stored and handled by the Local Security Authority Subsystem Service (LSASS) process in Microsoft Windows operating systems. The attacker should also dump these hash values from LSA using publicly available tools like lsadump.
- Having all the required master keys and token database file, install and deploy a windows machine and change the machine and user SIDs to the victim’s system SID by using available tools such as newSID.
- Overwrite the token database file, user and machine master keys with the ones copied from victim’s system. You would also need to find a way to update the DPAPI_SYSTEM value in LSA secrets of the Windows machine. Currently, this is the only challenge that I was not able to solve , but it should be possible to write a tool similar to lsadump which updates LSA secrets.
- When the above has been performed, you should have successfully cloned the victim’s software token and if they run the SecurID software token program on your computer, it will generate the exact same random numbers that are displayed on the victim’s token.
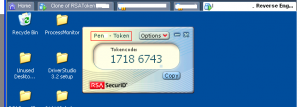
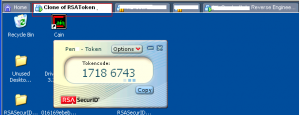
In order to demonstrate the possibility of the above mentioned attack, I installed and activated token A and token B on two separate windows XP virtual machines and attempted to clone token B on the virtual machine that was running token A. Taking the above steps, token B was successfully cloned on the machine running token A as shown in the following figures:
In order to counter the aforementioned issues, I would recommend the use of “trusted platform module” (TPM) bindings, which associates the software token with the TPM chip on the system (TPM chip for mobiles? there are vendors working on it).