Hacking PlayStation DualShock controllers to stream audio to their internal speakers.
Ciao a tutti.
Introduction
I didn’t really know what this project was going to be about and where or how it would end up. The only thing I know is that I started working on it because one day I was bored and having a chat with a friend of mine:
Your flat is like a Luna Park for nerds. Just look around and, I am sure, you’ll figure out what to do. — He said.
After that, I took the suggestion literally, I turned my head and…
Well, let’s avoid the cat. For now. :D
Then, looking at the dusty PlayStation4 (PS4) sitting on my desk, I start wondering if I could play music through the built-in speaker of the DualShock4 (DS4).
In addition to other features that will be described later on in this post, SONY also added a built-in speaker in the DS4. Yes, baby! The DS4 is also able to transmit audio data and voice while playing certain games (I.E. Grand Theft Auto 5) through the built-in speaker.
Audio from the speaker while playing GTA5
In GTA5 the audio comes from the speaker when the player receives/makes calls via phone, when followed by the police (LEDs also blinks blue and red) and when driving ambulances.
As an example, by calling a special number I have found on the internet when I was looking for cheats, it is possible to hear the sound of the old 56k modem connection from the speaker.
The number is 3465550155.
DualShock4 – Wireless Controller
DualShock is a gamepad with vibration-feedback and it was introduced in Japan in the late 90s by SONY. The reason for this name, perhaps, is it due to the use of two (Dual) vibration motors (Shock).
The gamepad has continued to evolve with each newest PlayStation release and, over time, several new features have been added to it.
- PlayStation – DualShock (SCPH-1200);
- PlayStation 2 – DualShock2 (SCPH-10010);
- PlayStation 3 – DualShock3 (SCPH-98050/CECHZC2);
- PlayStation 4 – DualShock4 (CUH-ZCT1/CUH-ZCT2).
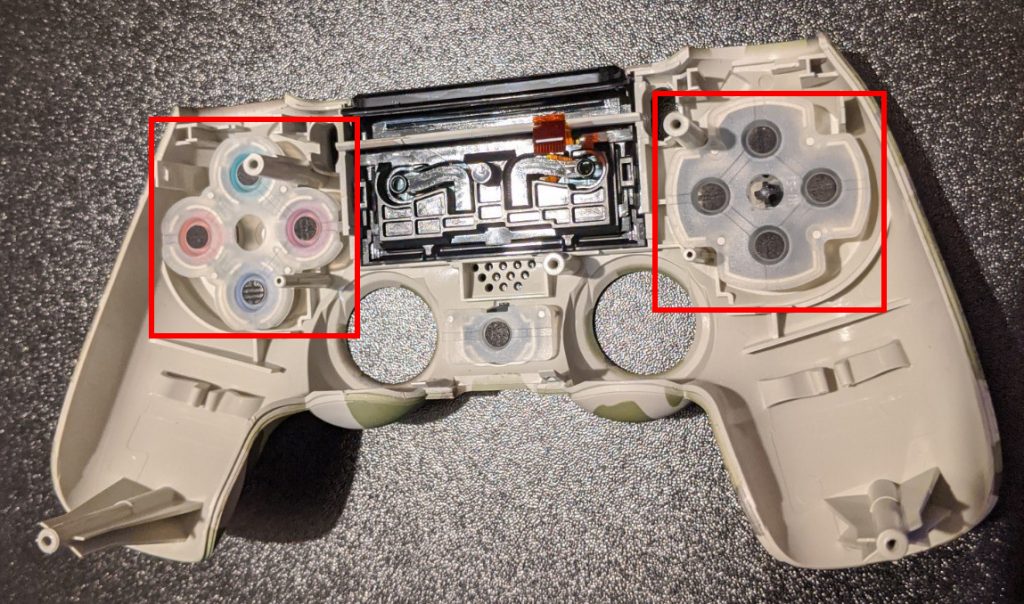
Below some DS4 features.
- Stereo headset jack (3.5 mm);
- Mono speaker;
- Touchpad;
- Lightbar with three LEDs;
- Micro-USB port and an extension port;
- Bluetooth;
- 6 axis motion sensing (3 axis accelerometer, 3 axis gyroscope);
- 2 Analog sticks;
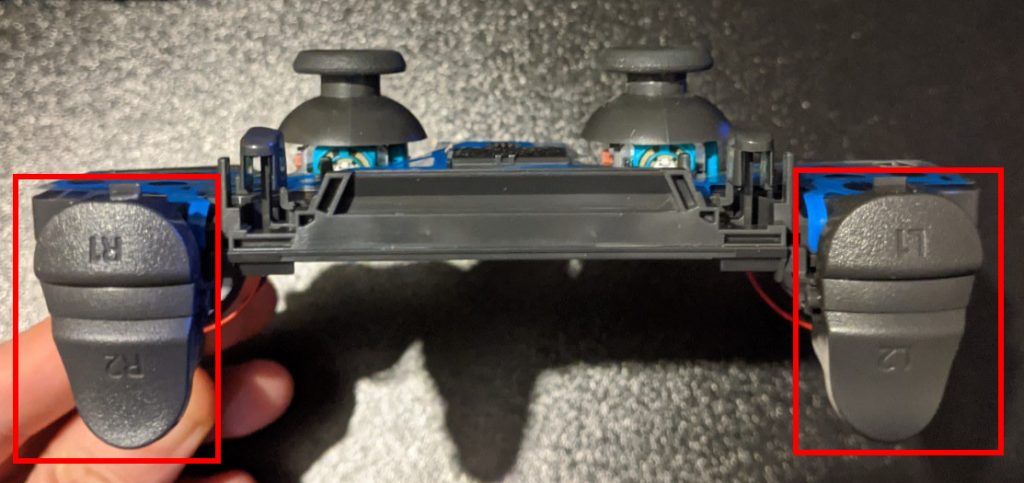
- 2 Analog triggers (L2, R2);
- 2 Pressure-sensitive buttons (L1, R1);
- 10 Digital buttons (Triangle, Circle, Cross, Square, L3, R3, PS, SHARE, OPTIONS, Touchpad);
- Digital directional buttons;
For more info refer to https://en.wikipedia.org/wiki/DualShock.
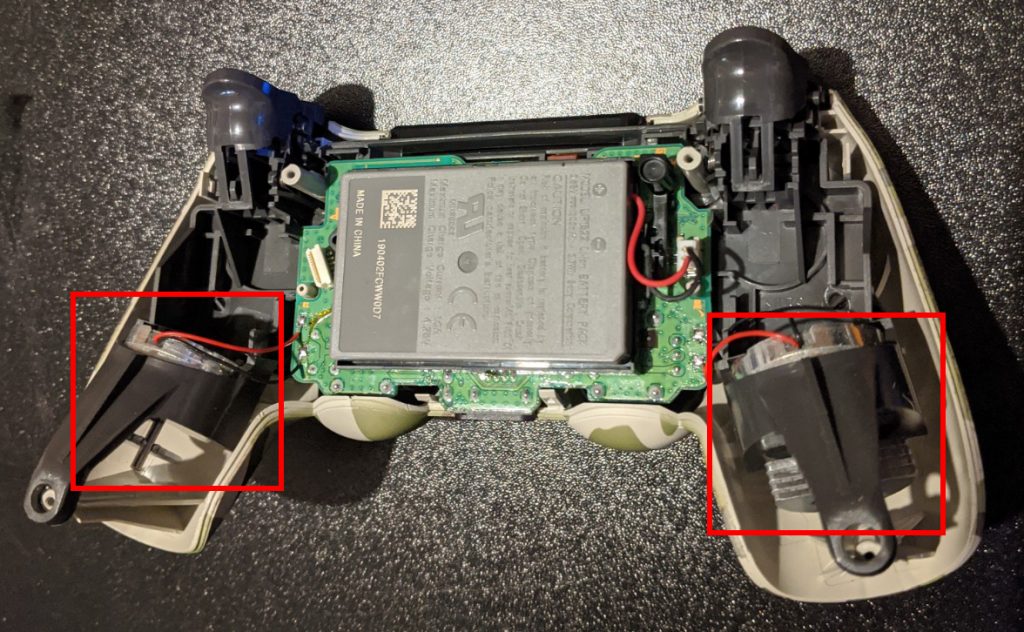
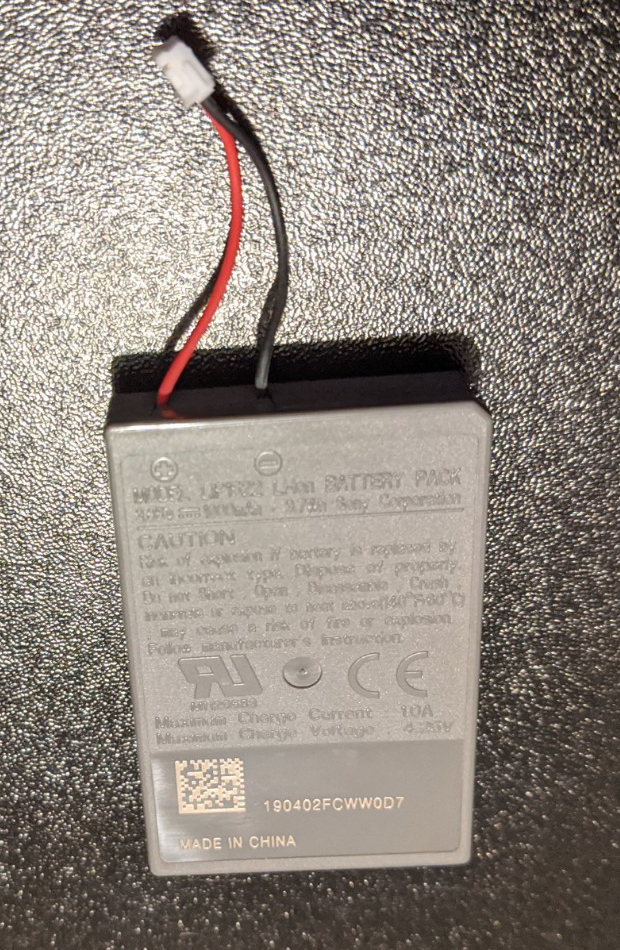
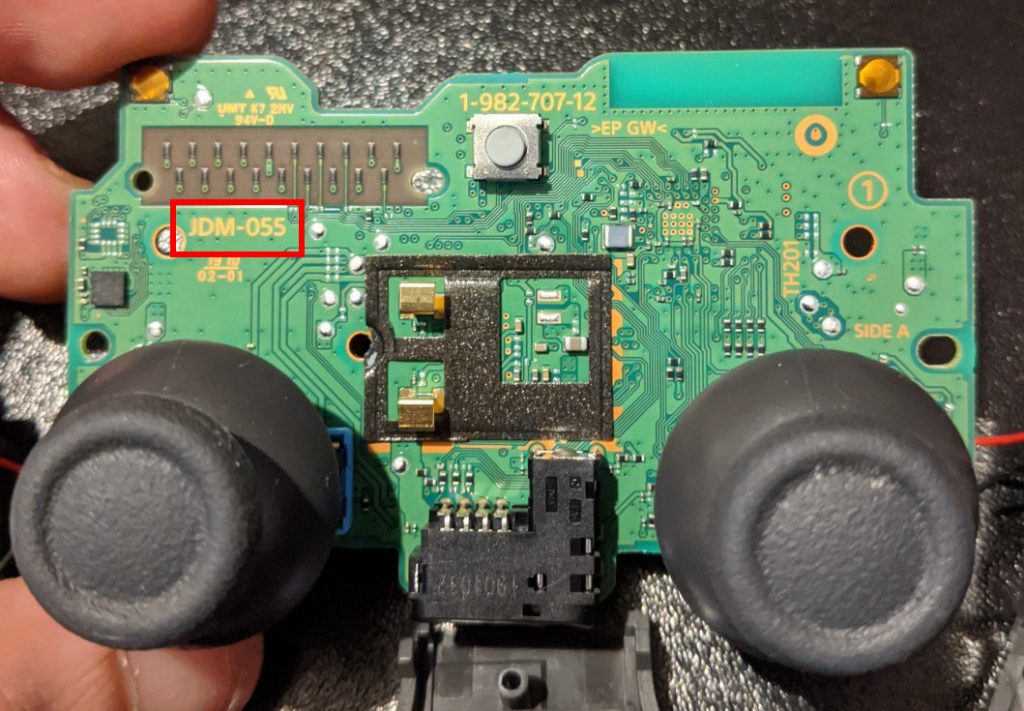
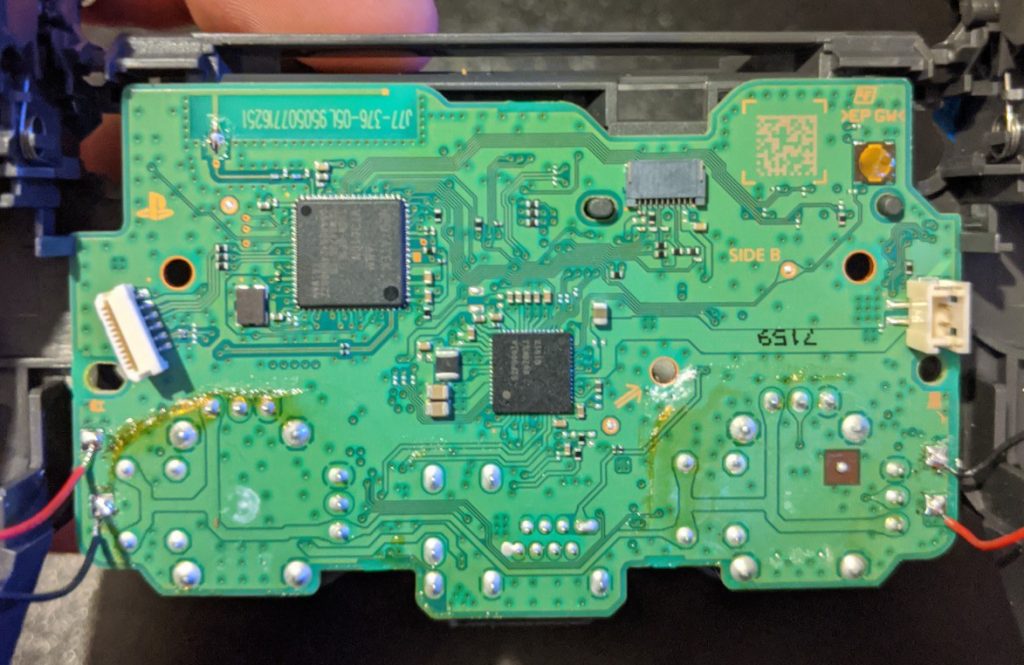
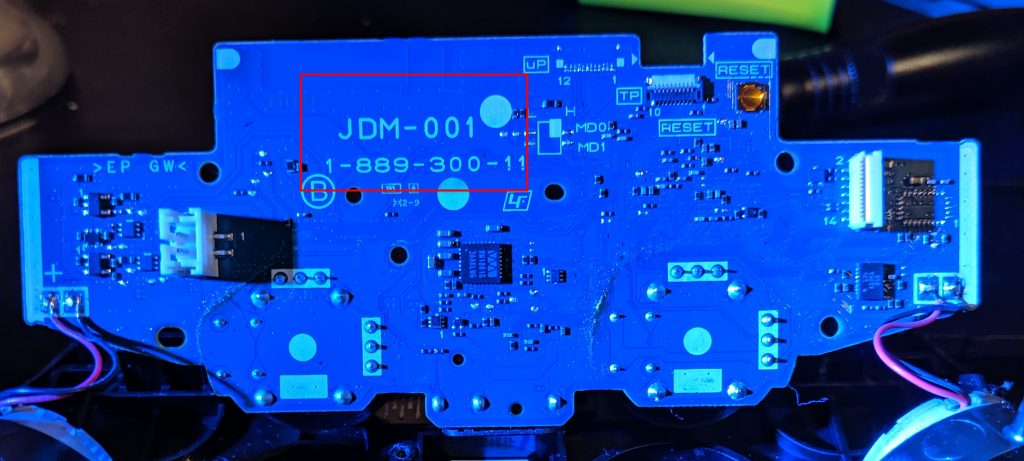
Teardown ds4 v2 (JDM-055)





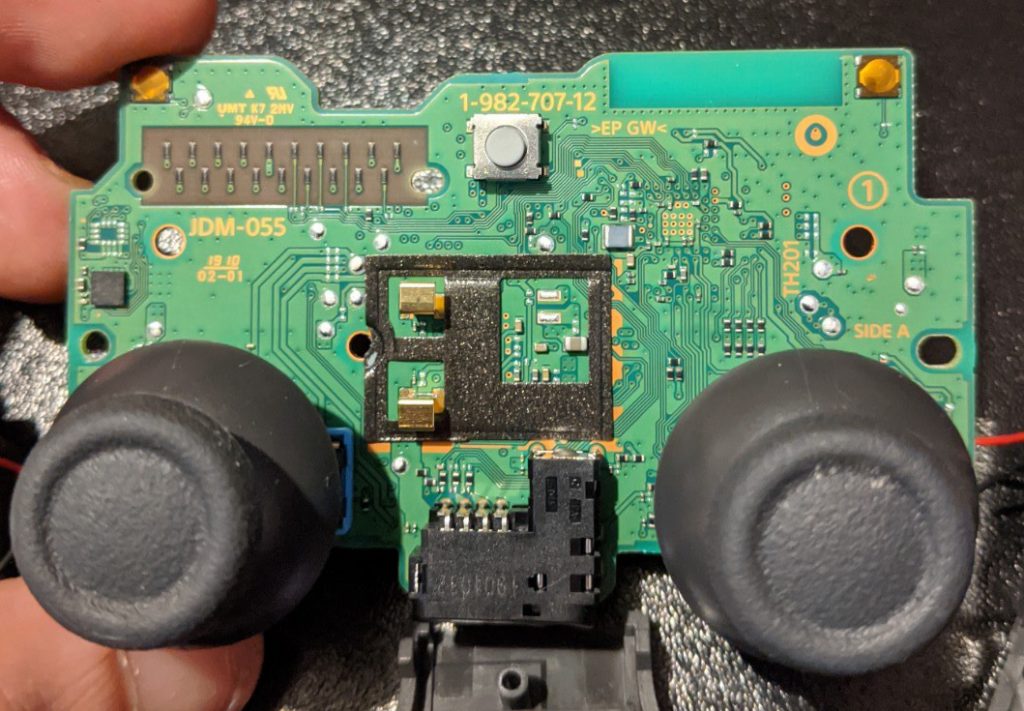
Models & PCB
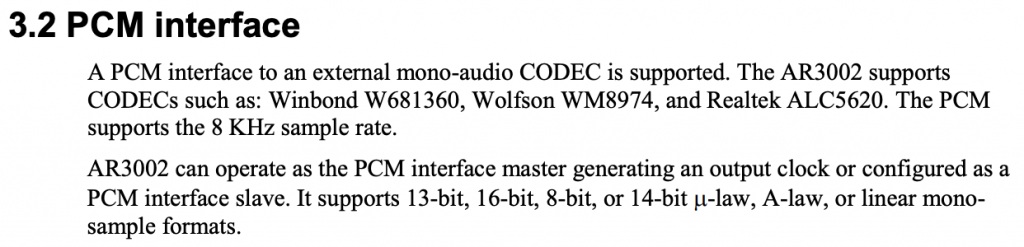
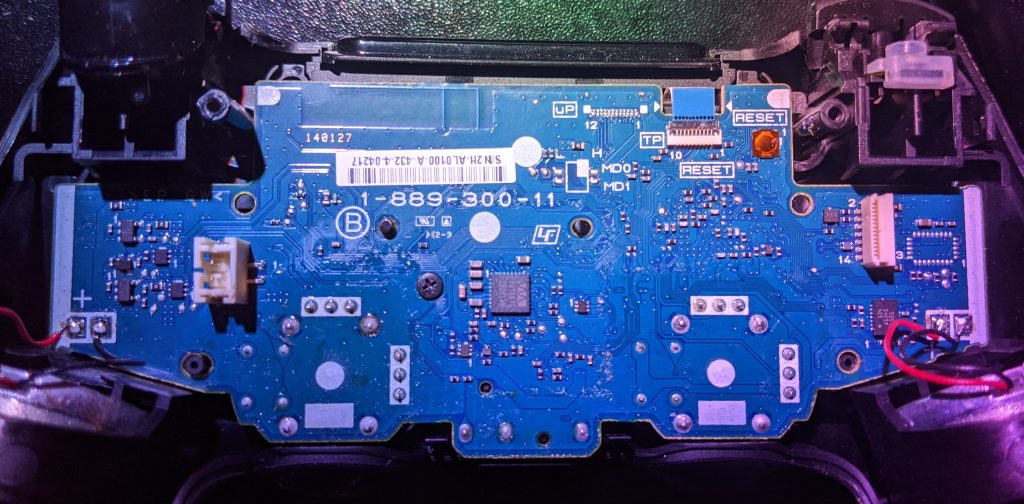
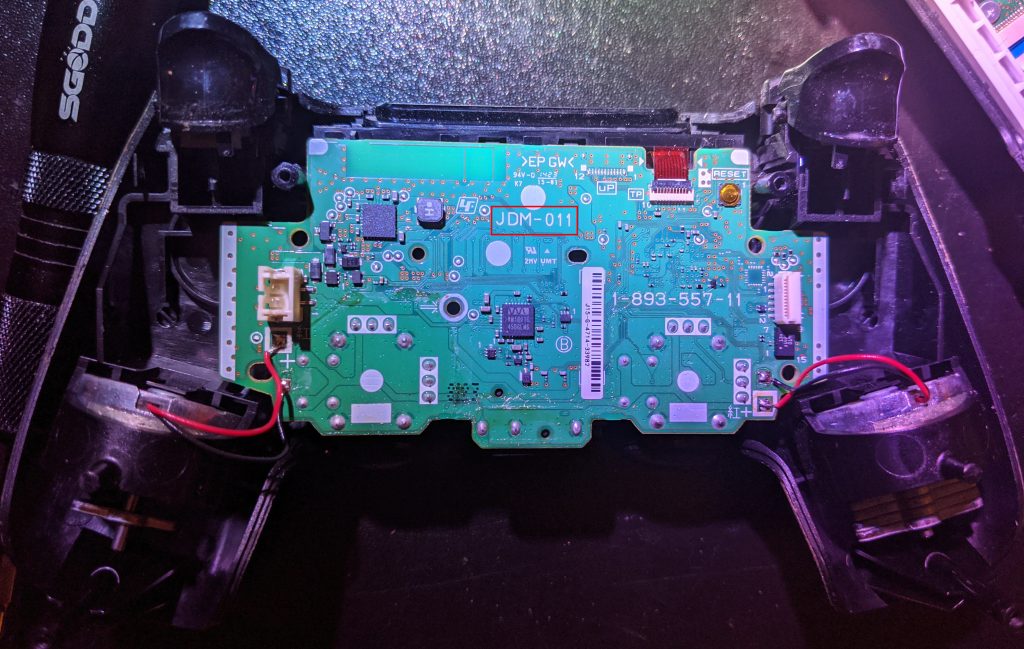
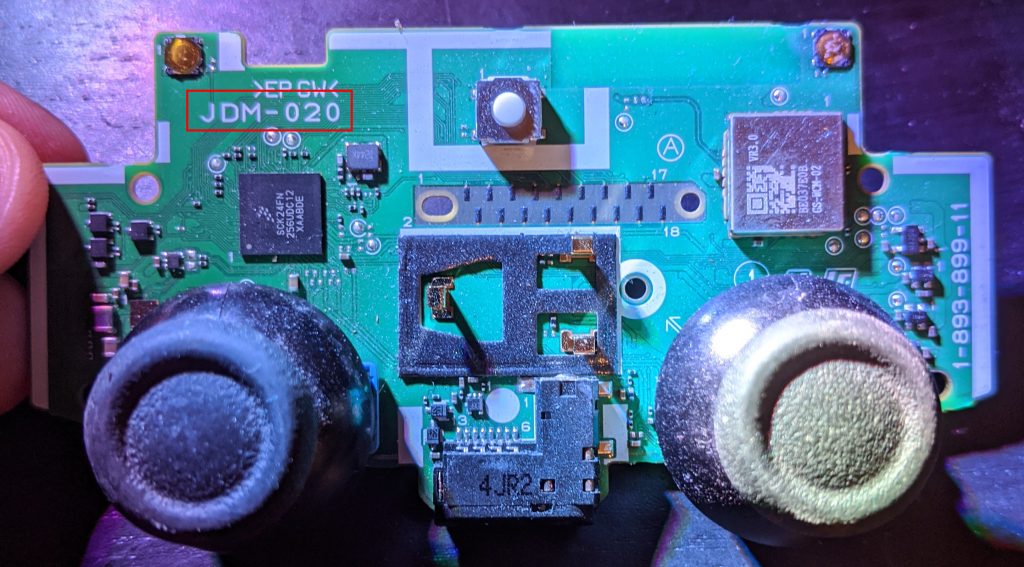
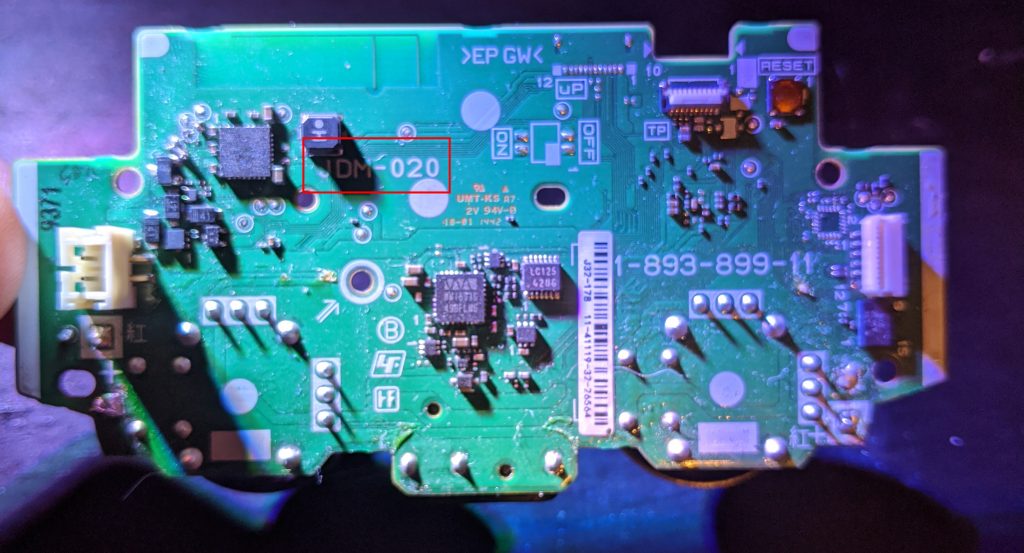
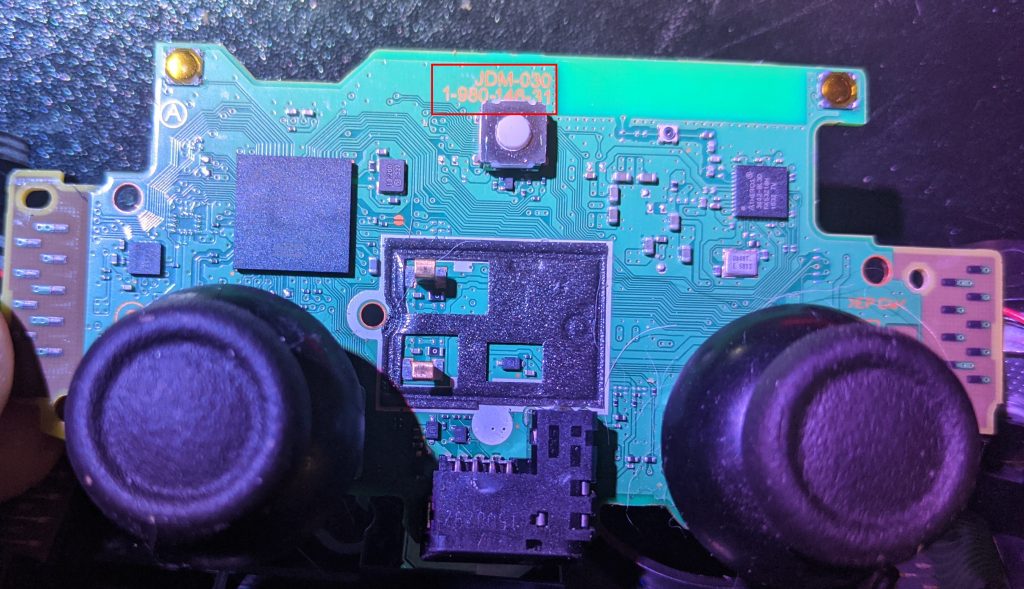
So far there are seven versions of the DS4 controller PCB (JDM-001, JDM-011, JDM-020, JDM-030, JDM-040, JDM-050, JDM-055). Each version belongs to a different generation. The second generation was confirmed and released by SONY in September 2016 with more features and improvements (Including USB communication, longer battery life and the ability to see the light bar from the top of the touchpad).
First Generation PCB or DualShock V1 (CUH-ZCT1) PCB:
- JDM-001;
- JDM-011;
- JDM-020;
- JDM-030.
Second Generation PCB or DualShock V2 (CUH-ZCT2) PCB:
- JDM-040;
- JDM-050;
- JDM-055.
Pairing and Connecting a DualShock 4
The DS4 supports two modes:
- Computer mode (Pair it with a computer);
- PS4 mode (Pair it with a PS4).
In order to pair the DS4 with a computer, press and hold the PS and SHARE buttons at the same time until the light blinks twice in quick succession rapidly. Proceed to pair/connect the computer with the joypad once it appears in our nearby-Bluetooth-devices-list. The device doesn’t require any passcode. In case it asks for a passcode try: 0000 or 1234.
By using kali 2019.4 I could see that the joypad was recognized as an audio device. Good start, but no audio output.
To retrieve more information about the device I used Bluetoothctl, a command-line interface of the bluez-utilities package.
To list nearby devices we first open Bluetothctl, then we start the scan. This could be done by using the below commands.
$ sudo bluetoothctl [bluetooth]# scan on [bluetooth]# agent on [bluetooth]# default-agent [bluetooth]# scan on
With the command “pair” the DS4 gets paired but then dies after a few seconds and it needs to be turned ON again. Skip the pairing part and just use “connect”. This will mitigate the issue.
[bluetooth]# connect 00:11:22:33:44:55
Once the connection has been made, the controller will be present in the system as a file: /dev/hidraw1. The below command will return some details about the device.
[Wireless Controller]# info 00:11:22:33:44:55
At this stage, by analyzing the output form Bluetoothctl, we can understand which kind of peripheral we are dealing with based on its Class of Device (CoD).
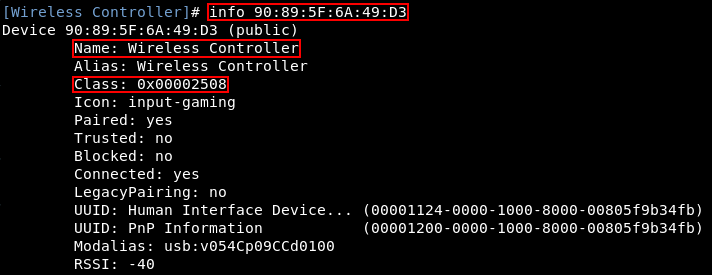
The DS4 I was testing had as Class of Device (CoD): 0x2508.
- Major Service Class: Limited Discoverable Mode;
- Major Device Class: Peripheral (Mouse, Joystick, Keyboards, …);
- Minor Device Class: Gamepad.
Based on the above information, there was no way to think of the DS4 as a custom speaker. Very disappointing.
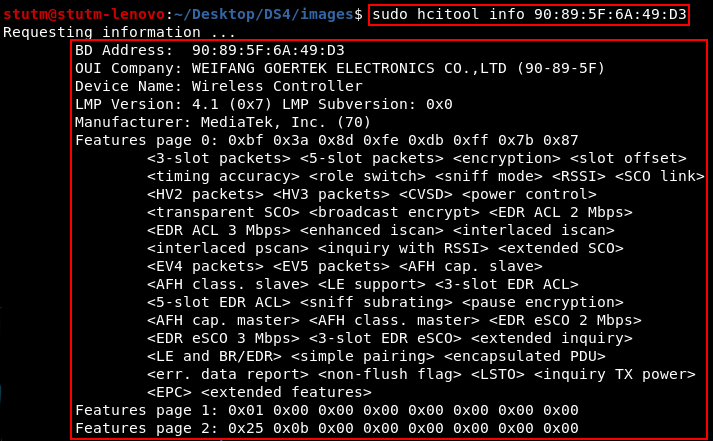
A great number of details, including the manufacturer and all the DS4 features, could be obtained by using a bluez-utility package named hcitool.
Note: The DS4 should already be paired and connected with the computer.
sudo hcitool info 00:11:22:33:44:55
I thought that maybe the speaker is only used in PS4 mode, so I tried to sniff some BT traffic to better understand how the PS4 sends audio data to the DS4. For this step, the only missing part was the PS4 Bluetooth MAC address and the link key specially generated for that DS4.
I tested a few tools (BLEAH, Bettercap, Bluetoothctl) to discover the PS4 BT MAC address but no luck. It seemed hidden and/or not discoverable.
I was about to open the PS4 (Usually, there is a sticker on the BT module which shows the MAC address) when, fortunately, I found this article: https://blog.gimx.fr/hci-uart-sniffer/.
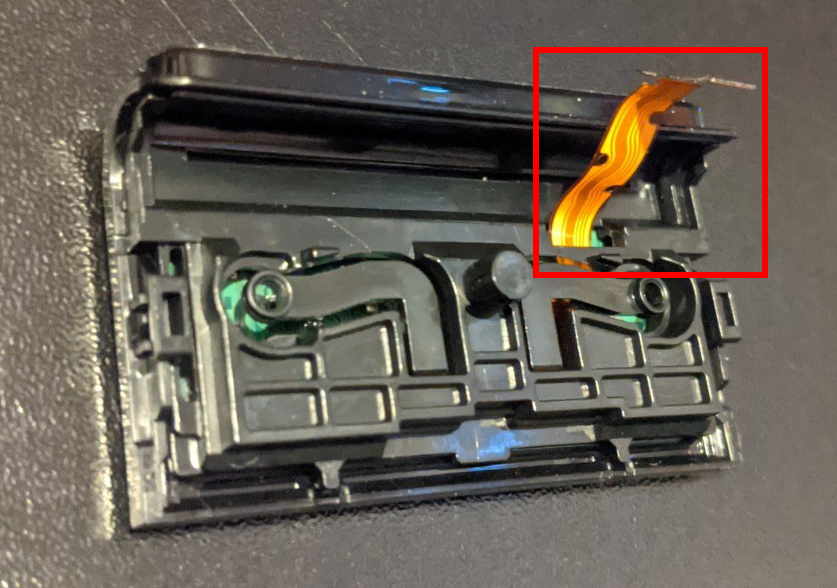
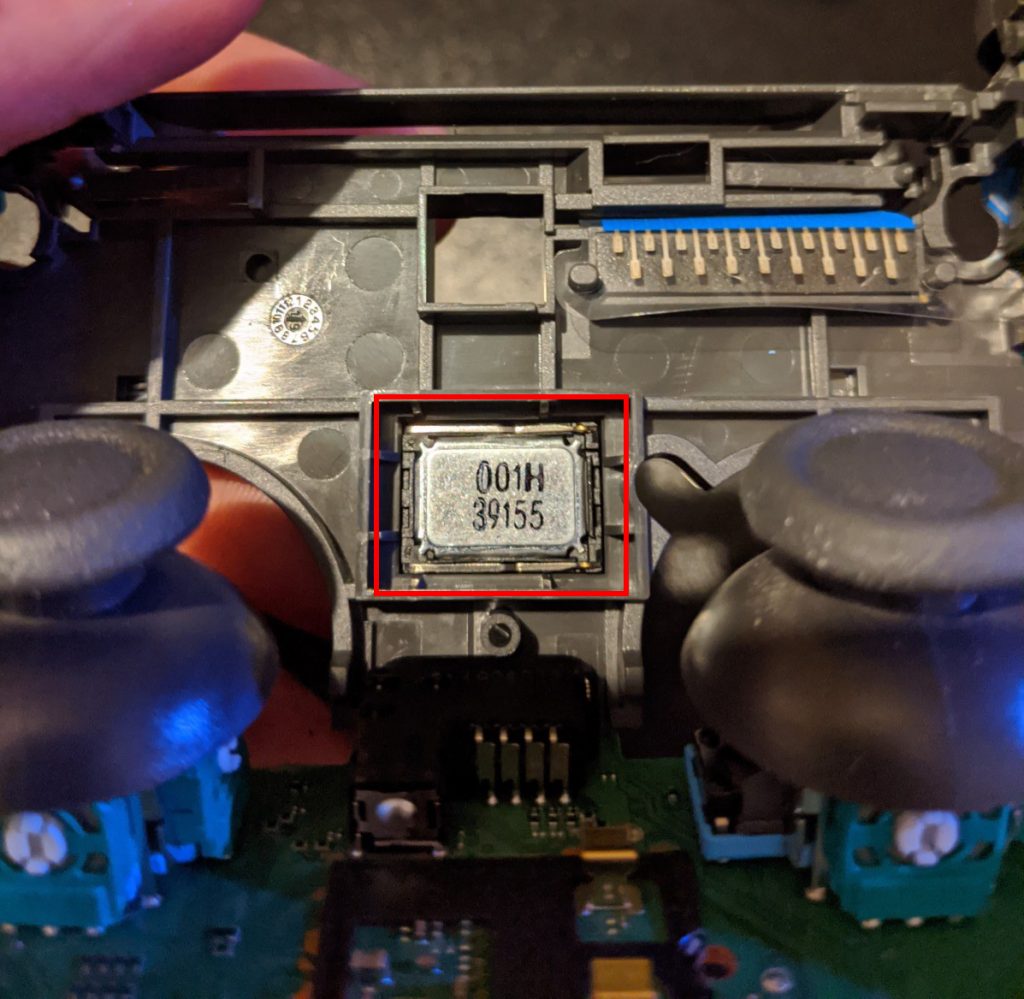
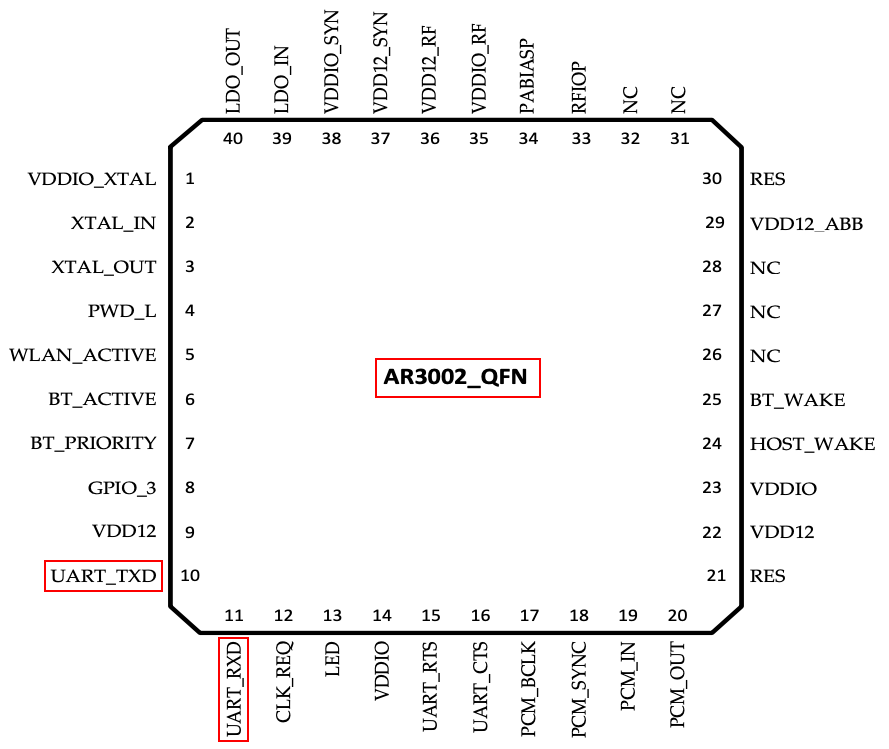
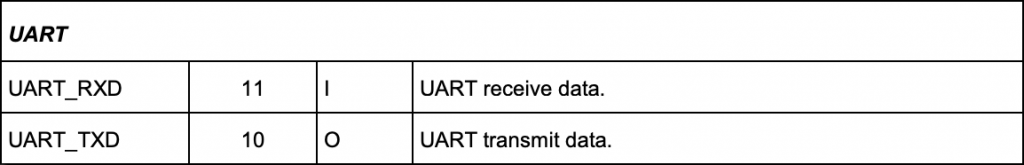
WOW! The Qualcomm Atheros AR3002 module of the DualShock V1 (CUH-ZCT1) has one of the earliest modes of communication applied to computers: UART (Universal Asynchronous Receiver/Transmitter).
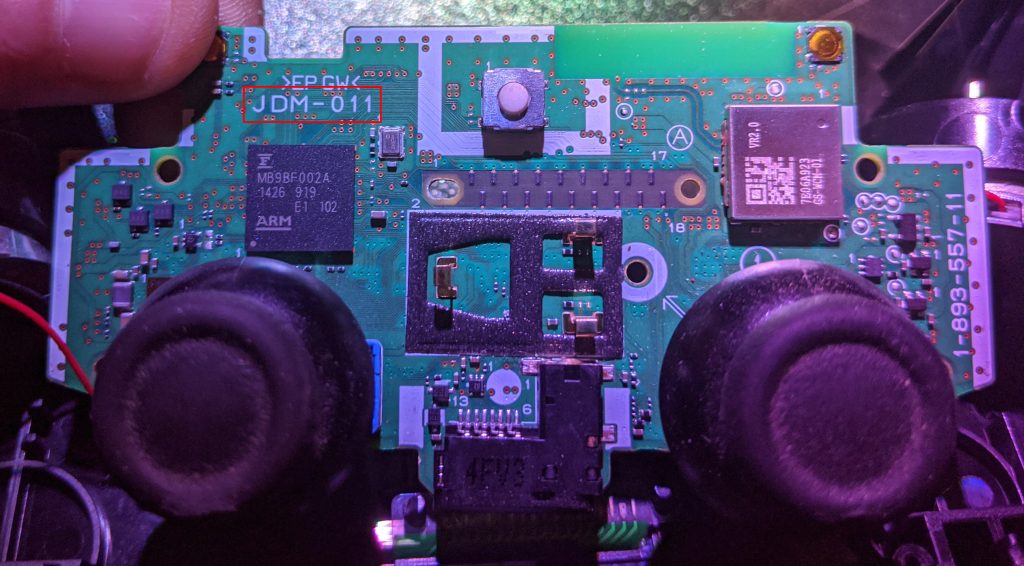
AR3002 – Bluetooth v4.0 UART HCI
AR3002 features
- Single-chip Bluetooth v4.0 solution;
- Bluetooth low energy dual-mode radio;
- Supports both Class-2 (up to +4 dBm) and Class-1 (up to +10 dBm) operation;
- Standard HS-UART HCI interface;
- 1.2 V linear voltage regulator (LDO);
- Integrated 32-bit CPU with 128 Kb data RAM and 512 Kb program ROM;
- On-chip low power oscillator (LPO);
- On-chip one-time programmable (OTP) memory;
- WLAN coexistence interface;
- Audio CODEC using PCM interface.
More details about the AR3002 module are available on this PDF.
Pulse-code modulation (PCM), is the standard method of encoding used for uncompressed digital audio.
Good, the audio is definitely sent (Or streamed) via Bluetooth.
Let there be shock!

I started buying joysticks here and there with the hope of finding a DS4 V1. Over a few months, I managed to collect a few DS4s, of which four were from the first generation, one was from the second generation and the others were duplicates. I am still missing JDM-040 and JDM-050. It would be great having the full collection to hang up on a wall. I am not really looking for them but, if you have one of the above-mentioned PCBs and you wanna donate it… ping me.
Below is my collection.
- JDM-001;
- JDM-011;
- JDM-020;
- JDM-030;
- JDM-055.

HCI UART Sniffer
After promising rewards, tell-a-friend-to-tell-a-friend, and wasting money because of bad sellers… I finally obtained the JDM-001!
Below are some instructions on how to retrieve data (Sent from the PS4 to the DS4) from the UART of the AR3002 module using the RX of the Arduino Uno and the FTDI232. This technique is also known as a “Double RX Attack” but I like to call it “Hard-Proxy”. It is literally a physical (Hardware) proxy.
Requirements
- 1 PS4;
- 1 DS4 V1;
- GTA5 (Or any other game that uses the built-in speaker feature);
- 1 FTDI232 – USB to TTL serial converter adapter module;
- 1 Arduino Uno;
- 1 Soldering Iron;
- Wires.
Note: The Arduino Uno doesn’t need the ATMega chip.
Additionally, turn ON the PS4 and the DS4 just after launching the sniffer tool.
Arduino Uno FTDI232 DS4
-------------------------------------------------------------------
RX UART_TXD
Pin 2 TX UART_RXD
GND GND GND
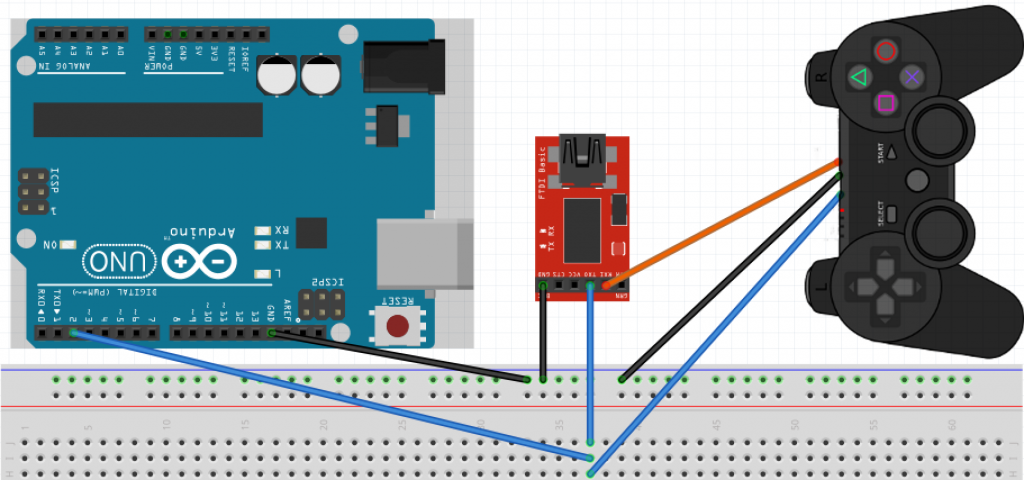
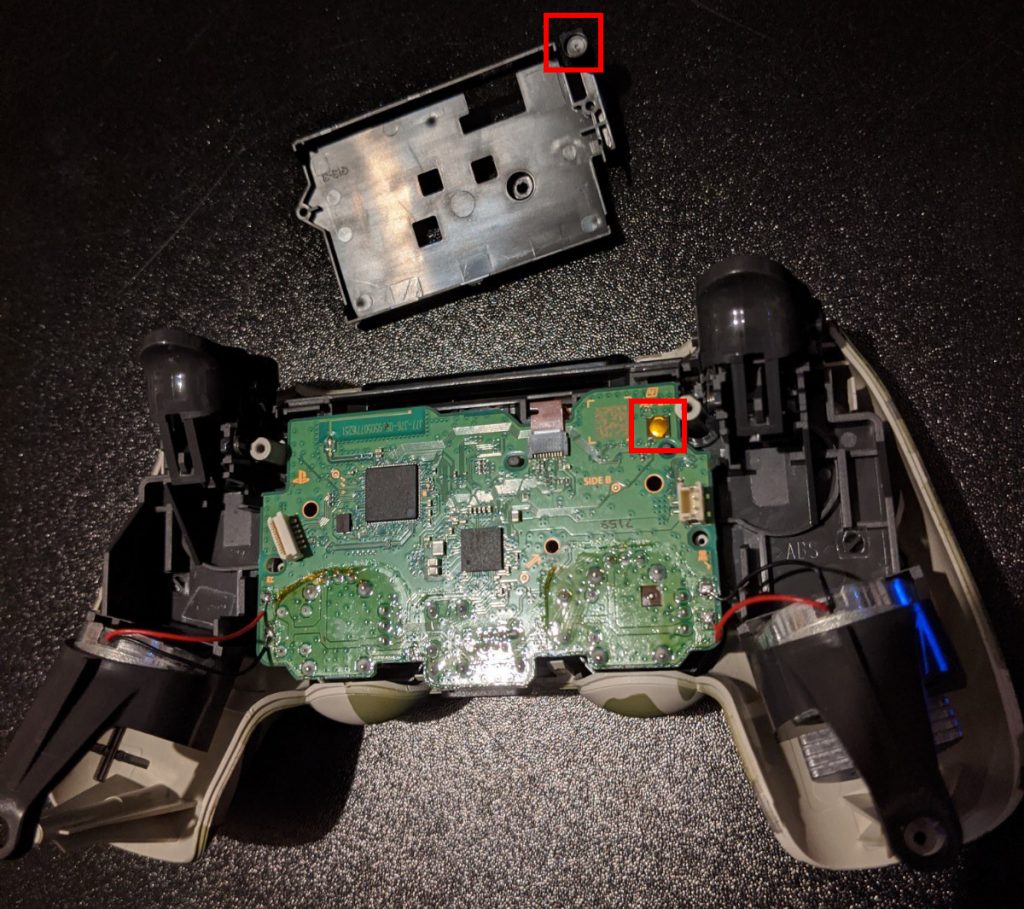
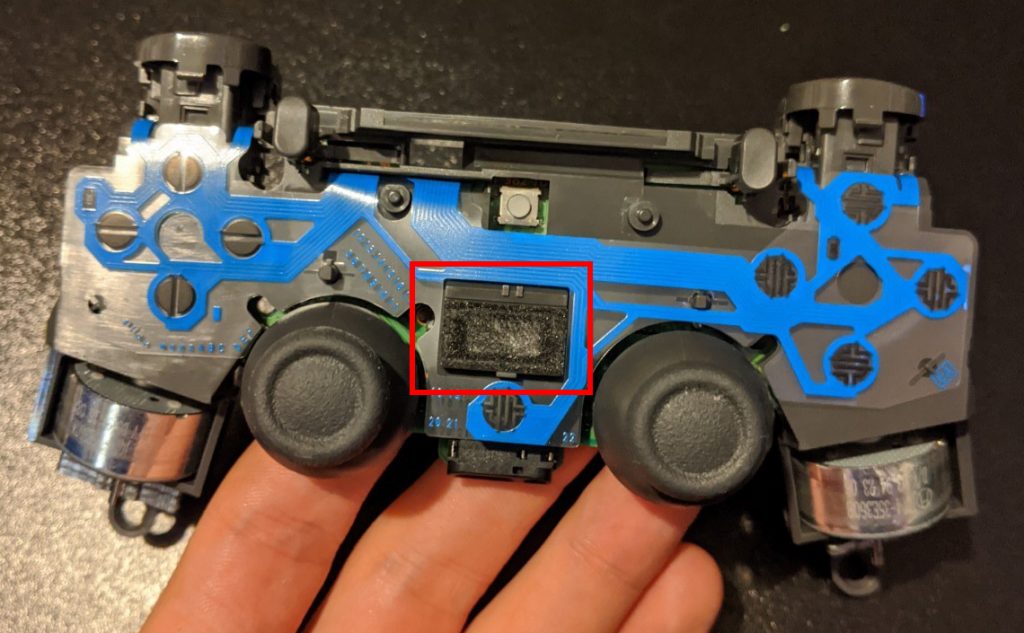
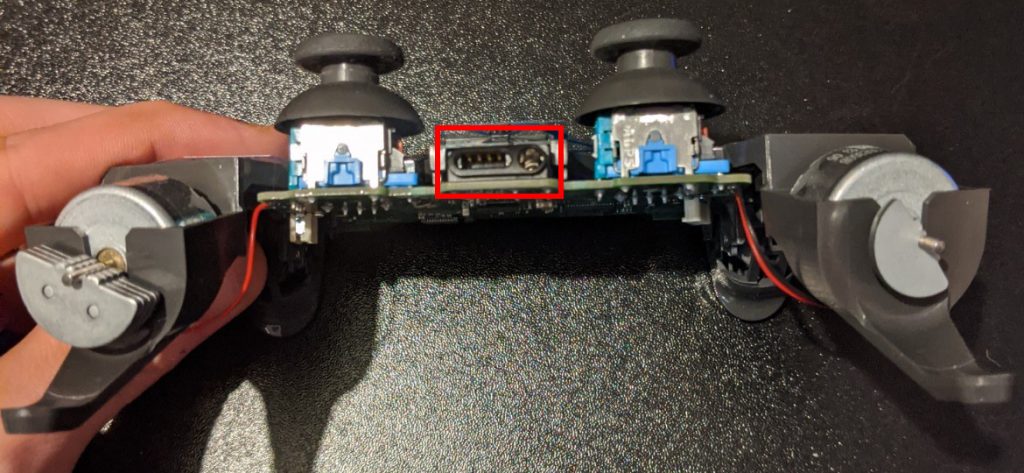
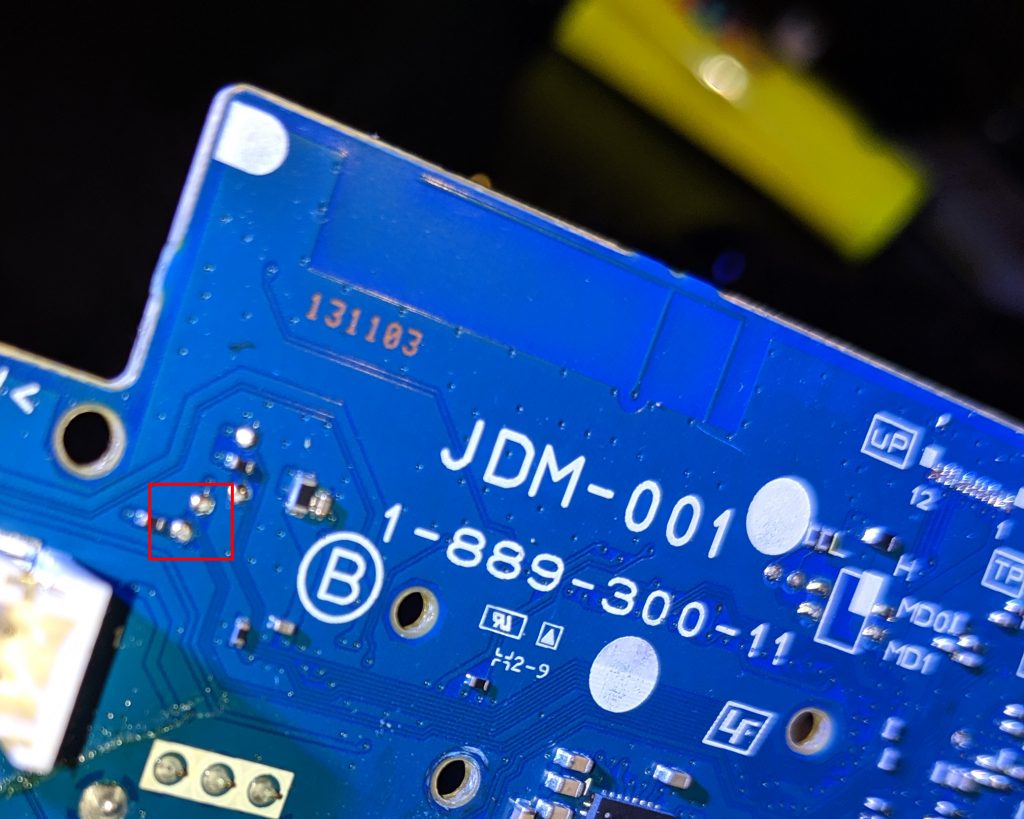
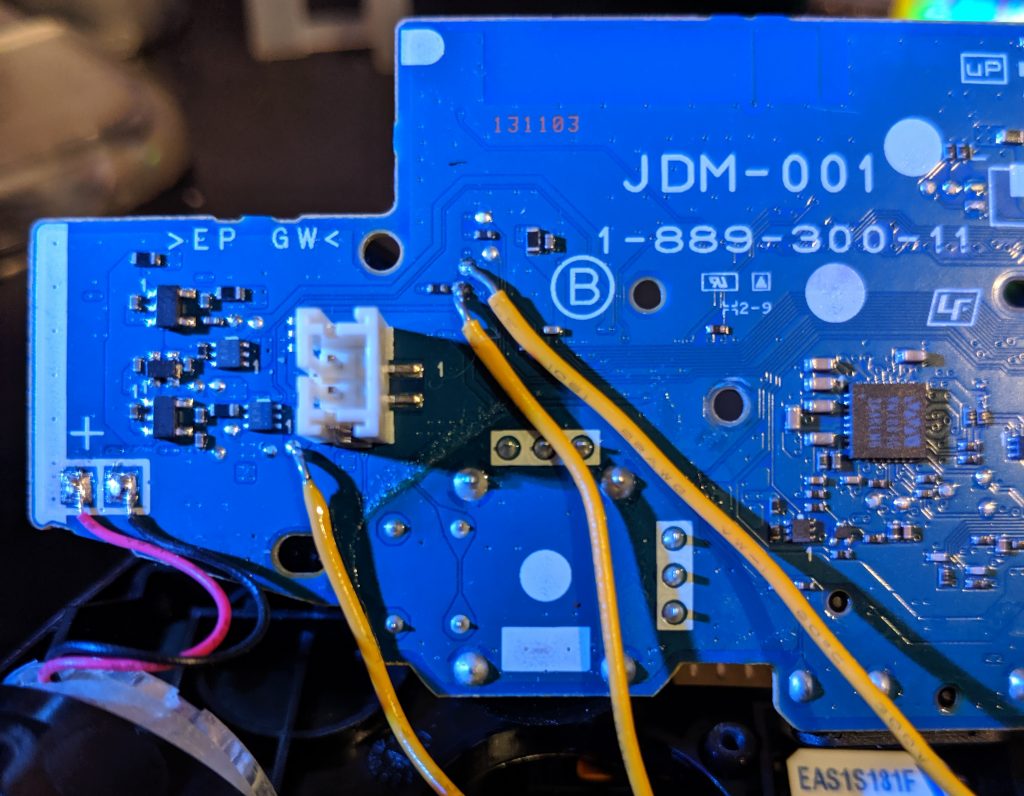
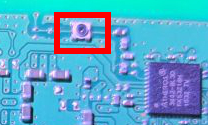
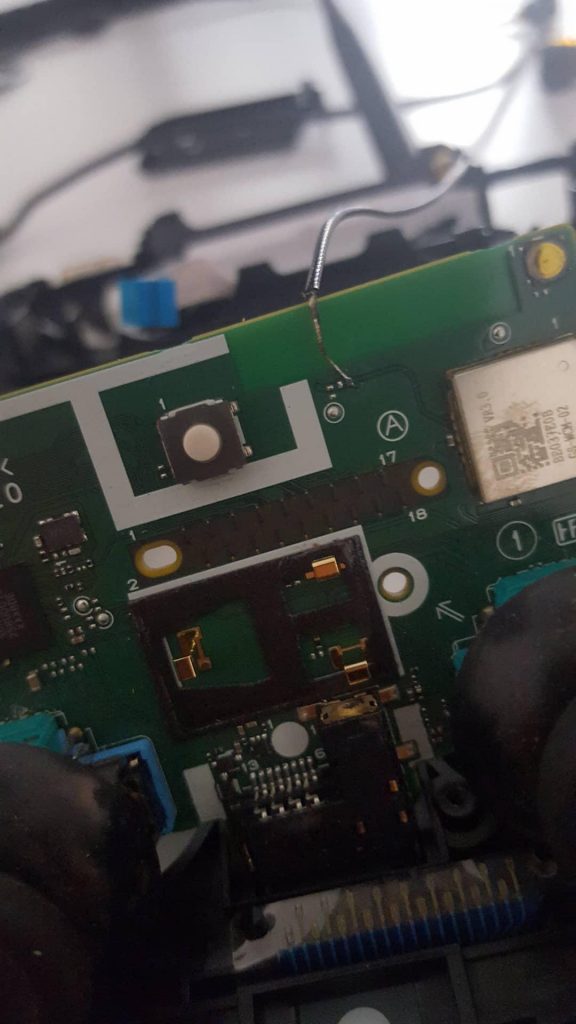
The following image shows where the pin 10 (UART_TXD) and 11 (UART_RXD) of the AR3002 were located.
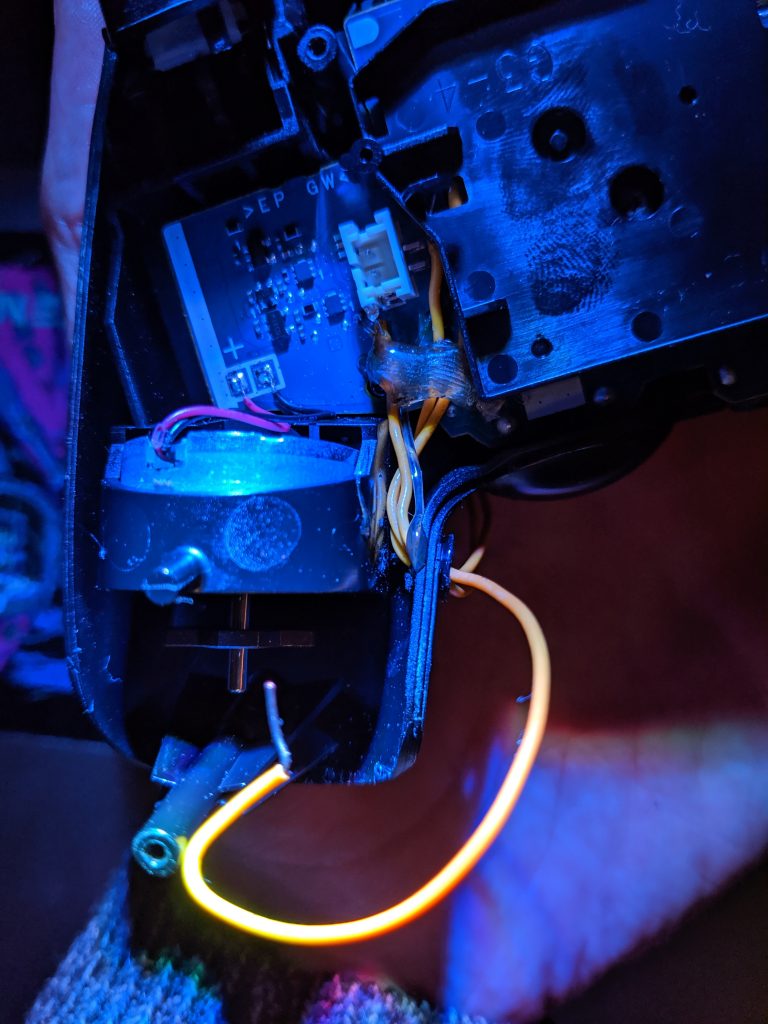
The soldered wires were easily detached and I was afraid of destroying the piece of art that is the controller. So, I made a hole in the DS4 shell for wires to pass through. Finally, despite having a spare one, I used hot glue to stick everything on the PCB before closing the case. Better safe than sorry.
After re-building the DS4, I connected it to the PS4 using its Micro-USB port. Then, I plugged the Arduino Uno and the FTDI232 to my computer. Finally, I launched the sniffer tool from the post mentioned above.
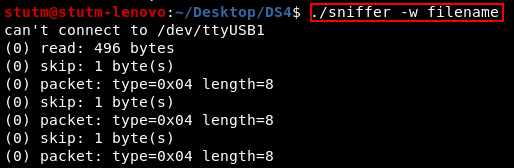
I opened the generated output with Wireshark and…

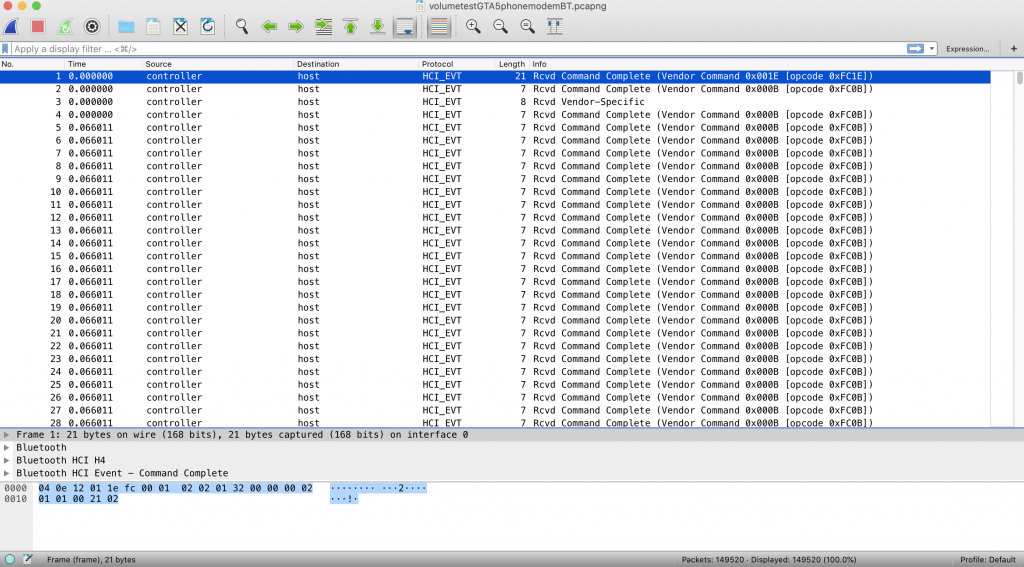
Below are some actions made by the PS4.
Note that the USB wire was still plugged in. The below image shows a few actions taken by the PS4 before disconnecting the DS4 (USB).
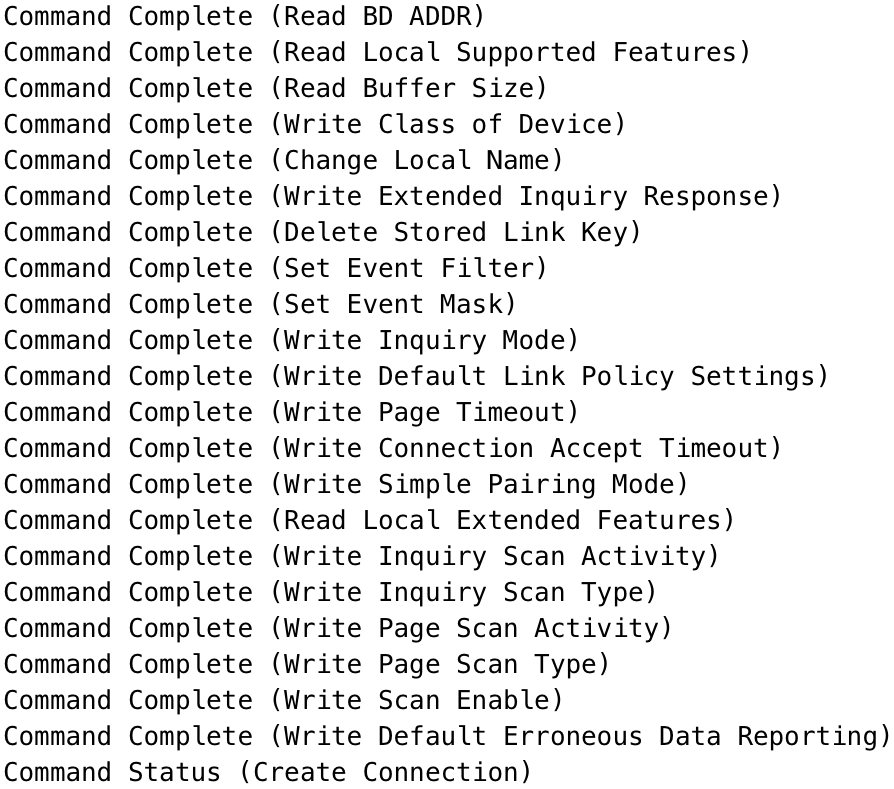
From there on, the DS4 was set as Slave and it requested the BT link key to the PS4. Then, the encryption changed based on the link key received.
YaY! Another important thing to highlight is that the PS4 also assigned a new Class of Device to the DS4: 0x0c24.
- Major Service Class: Limited Discoverable Mode, Rendering, Capturing;
- Major Device Class: Audio;
- Minor Device Class: Wearable Headset Device.
According to this very useful page, the DS4 was in PS4 mode.
Moreover, by simply unplugging the DS4 from the PS4 (USB) I noticed an error in Wireshark. After that, the PS4 started the BT pairing/connection process with the DS4. The error said: Write Default Erroneous Data Reporting.
This Hard-Proxy process could be avoided, once you have obtained the link key and the PS4 BT MAC Address, by using the tool l2cap_proxy. Below are some example commands.
sudo service bluetooth stop
sudo echo "{bdaddr} 4 0" >> /var/lib/bluetooth/{dongle bdaddr}/linkkeys
sudo service bluetooth start
sudo service bluetooth stop
sudo hciconfig hci up pscan
sudo ./l2cap_proxy {master-bdaddr} {dongle-bdaddr} {device-class}
HID Reports
Master and Slave were communicating with each other by sending and receiving a bunch of bytes per time. These frames are also called reports (Or packets). Each report contained instructions related to the game action that was happening at that moment. I mostly focused on reports that contained information about rumbles, LEDs, and sound.
Report with id 11
Number of bytes: 78.
It contains rumbles, LED color and volume headset speakers/built-in speaker/mic.
11 c0 20 f0 44 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 43 43 00 4f 85 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 64 e4 c6 3b
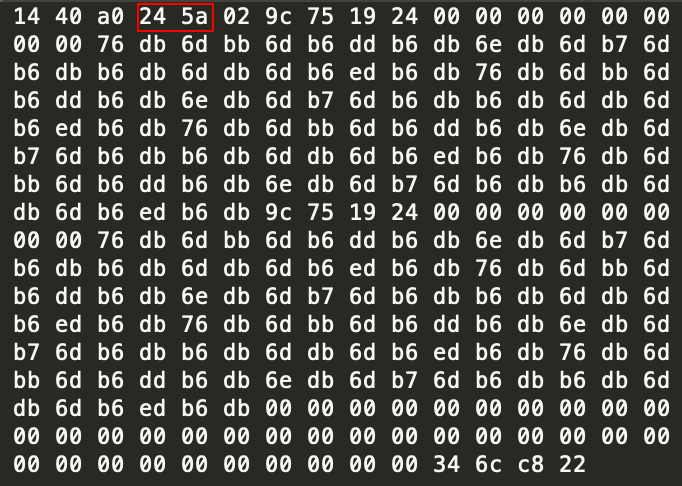
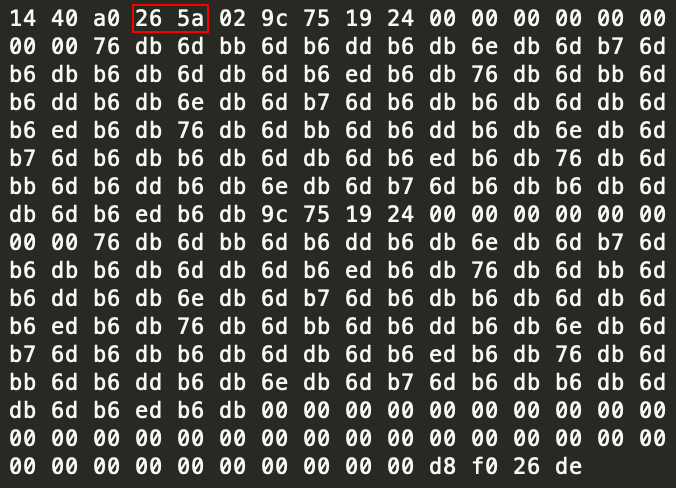
Report with id 14
Number of bytes: 270.
It contains sound.
14 40 a0 3c 02 02 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ba 0e 08 5d
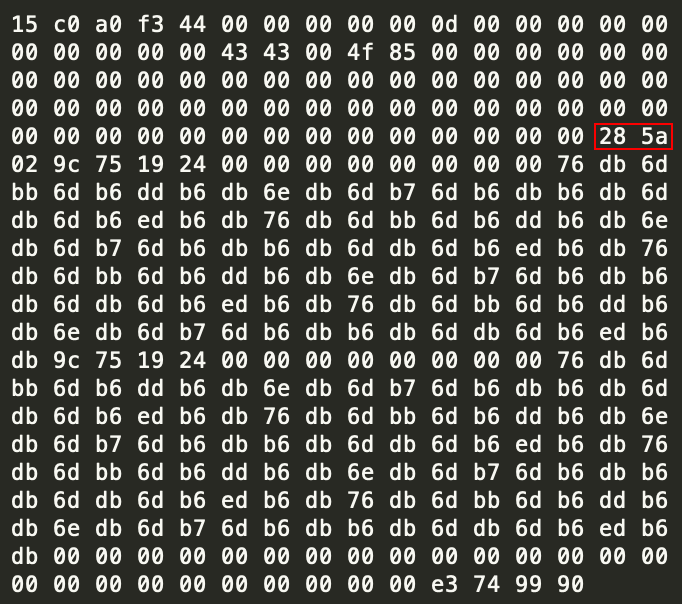
Report with id 15
Number of bytes: 334.
It contains rumbles, LED color, volume headset speakers/built-in speaker/mic, and sound.
15 c0 a0 f3 44 00 00 00 b0 50 00 00 00 00 00 00 00 00 00 00 00 43 43 00 4f 85 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 e0 b0 02 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 19 f8 d2 1c
Report with id 17
Number of bytes: 462.
It contains sound.
17 40 a0 24 7a 02 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 00 00 00 00 30 71 71 87
Report with id 19
Number of bytes: 567.
It contains rumbles, LED color, volume headset speakers/built-in speaker/mic, and sound.
19 c0 a0 f3 44 00 00 00 00 00 0d 00 00 00 00 00 00 00 00 00 00 43 43 00 4f 85 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 6a 37 02 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 9c 75 19 24 00 00 00 00 00 00 00 00 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 76 db 6d bb 6d b6 dd b6 db 6e db 6d b7 6d b6 db b6 db 6d db 6d b6 ed b6 db 00 00 00 00 00 00 00 00 00 00 00 00 00 00 51 11 9a 4f
REVERSING
I spent a few days understanding the meaning of each byte, how to modify them and why. Here’s the resulting breakdown:
buf[0] = 0x15; // Protocol Code buf[1] = 0xc0; // c0 Blueooth mode, a0 USB mode buf[2] = 0xa2; // transaction type (a=OUTPUT, 2 DATA) buf[3] = 0xf3; // LED/rumble motors: 0xf0 OFF, 0xf3 ON buf[4] = 0x04; // Unknown buf[5] = 0x00; // Unknown buf[6] = 0x00; // Rumble Right Power buf[7] = 0x00; // Rumble Left Power buf[8] = 0x00; // Red buf[9] = 0x00; // Green buf[10] = 0x40; // Blue buf[11] = 0x00; // LED Flash ON buf[12] = 0x00; // LED Flash OFF buf[13] = 0x00; // Unknown buf[14] = 0x00; // Unknown buf[15] = 0x00; // Unknown buf[16] = 0x00; // Unknown buf[17] = 0x00; // Unknown buf[18] = 0x00; // Unknown buf[19] = 0x00; // Unknown buf[20] = 0x00; // Unknown buf[21] = 0x43; // Vol Left buf[22] = 0x43; // Vol Right buf[23] = 0x00; // Vol Mic buf[24] = 0x80; // Vol Built-in Speaker buf[25] = 0x85; // Unknown buf[26] = 0x00; // Extended frames ... buf[77] = 0x00; // End Extended frames buf[78] = 0x00; // Frames counter buf[79] = 0x00; // End Frames counter buf[80] = 0x02; // Audio Header (24 Headset / 02 Speaker) buf[81] = 0x9c; // Syncword (ascii 156) buf[82] = 0x75; // 1110101 buf[83] = 0x19; // Bitpool (int 19) buf[84] = 0x24; // AUDIO DATA ... buf[329] = 0x00; // END AUDIO DATA buf[330] = 0x24; // CRC buf[331] = 0xc5; buf[332] = 0x3e; buf[333] = 0xfc; // END CRC
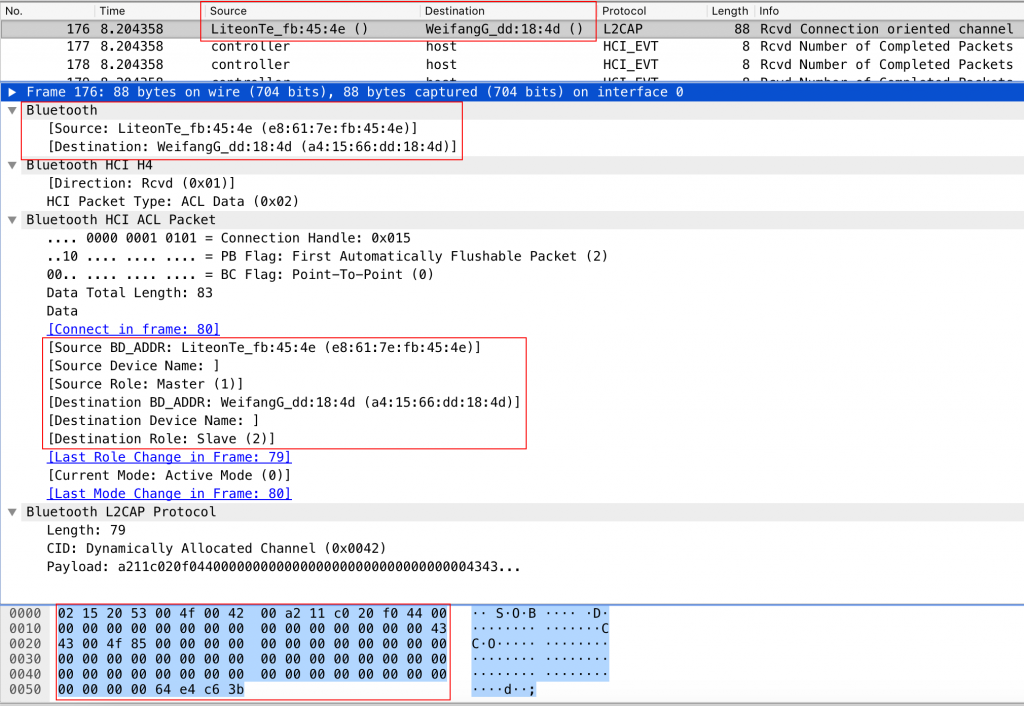
SBC Header
By looking at the reports listed above you will notice some constants, namely the successive bytes: 9c 75 19. This looks like the Bluetooth SBC header. SBC is a standard codec for transmitting audio via Bluetooth.
- 9c – Syncword (ASCII 156);
- 75 – 11 Frequency, 10 Blocks, 10 Channels, 0 Allocation Method, 1 Subbands (Binary 1110101);
- 19 – Bitpool (int 19).
More info is available on this page: https://www.psdevwiki.com/ps4/DS4-BT.
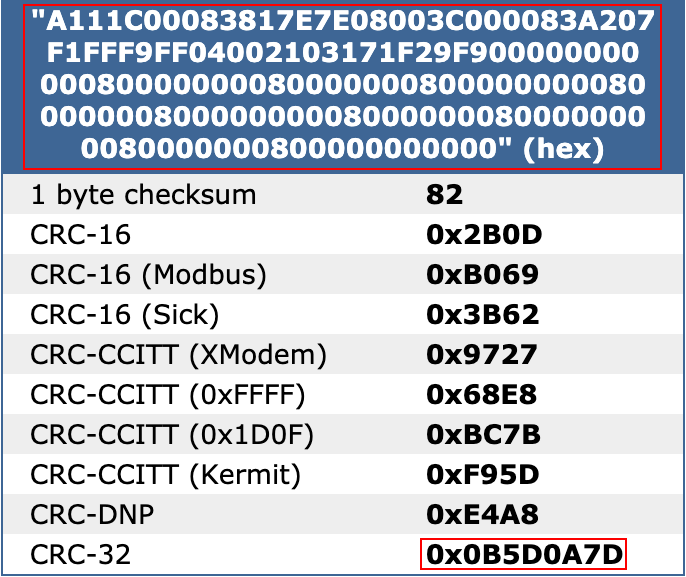
CRC-32
These four bytes are always at the end of the report to ensure that the packet is valid. Below is the CRC calculation breakdown of a string from a random report.
A111C00083817E7E08003C000083A207F1FFF9FF04002103171F29F90000000000080000000080000000800000000080000000800000000080000000800000000080000000800000000000
On the internet, there are countless projects that allow you to send bytes to the DS4 via Bluetooth. I tried a few of them; USB Host Shield 2.0 (needs additional HW) and ds4drv (doesn’t need HW).
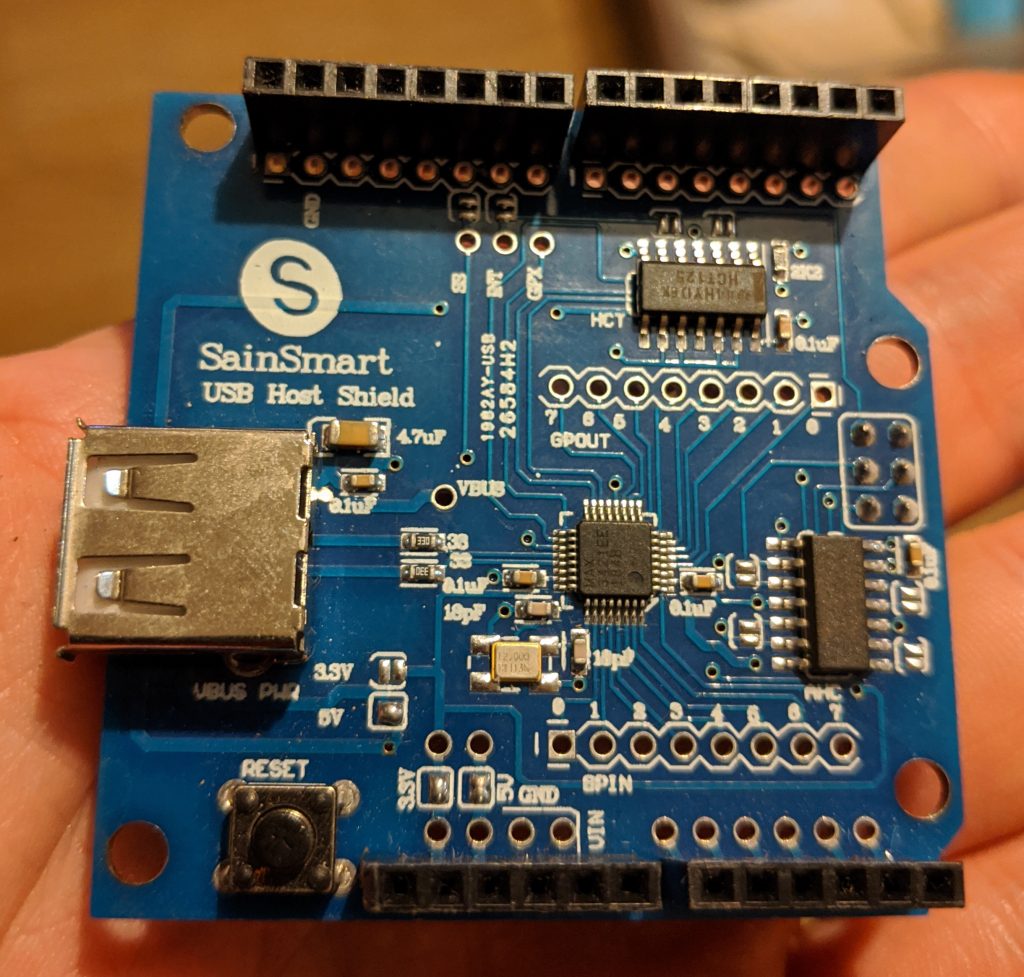
USB Host Shield 2.0
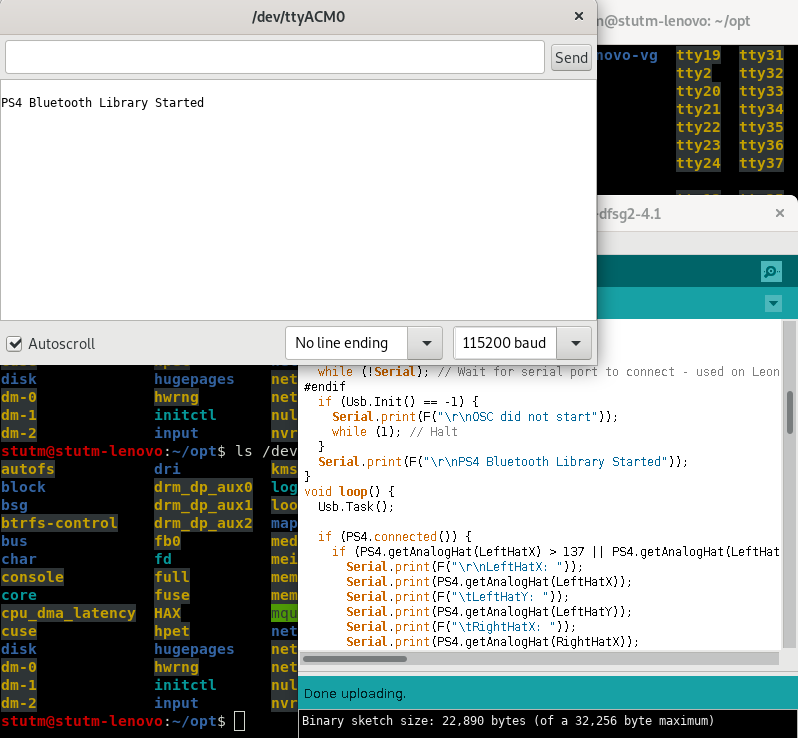
The USB Host Shield 2.0 is a board that allows you to connect a USB device to your Arduino. For example, for this experiment, I used a 4.0 Bluetooth dongle. The only thing to care about is to plug the USB Host Shield 2.0 into Arduino Uno and run the example code.
Everything worked perfectly at the first shot!
Requirements
- 1 USB Shield 2.0;
- 1 Arduino Uno;
- 1 USB Dongle 4.0;
- 1 DS4.
Refer to this page for the library and all the example code and here is where you can buy a USB Shield 2.0.
ds4drv
The same thing could be done by using a Sony DualShock 4 userspace driver for Linux named ds4drv.
For this, no hardware is required. Well, except for the DS4.
Some features of this driver:
- Option to emulate the Xbox 360 controller;
- Setting the LED color;
- Reminding you about low battery by flashing the LED;
- Using the trackpad as a mouse;
- Custom mappings;
- Settings profiles that can be cycled through with a button binding.
Installation instructions:
$ git clone https://github.com/chrippa/ds4drv.git $ cd ds4drv $ sudo python setup.py install
This command will set the LEDs color to red.
ds4drv --led ff0000
Yes, amazing but… I wanted the sound and because none of those projects I tested was the right one, I decided to write my own script.
DUAL-POD-SHOCK
I wrote a C program to write bytes into the HID of the paired DS4. Cool! With my script, I was able to change the color of the LEDs. The vibration motors were working without problems too. I tried sending one of the reports with id 15 I grabbed from the GTA5 dump, but the only DS4 output was a poot (PRRRRRRRRRRRRRR).
By looking at the reports again I noticed something weird. One of the bytes seemed to be a counter. Apparently, the counter was increasing itself by 2 on each audio frame.
The following code is an example to reproduce the counter with three lines of python.
int i;
for(i=0;i<0xffff; i+=2)
printf("%02x%02x\n", i & 255, (i /256) & 255) //endian reversed
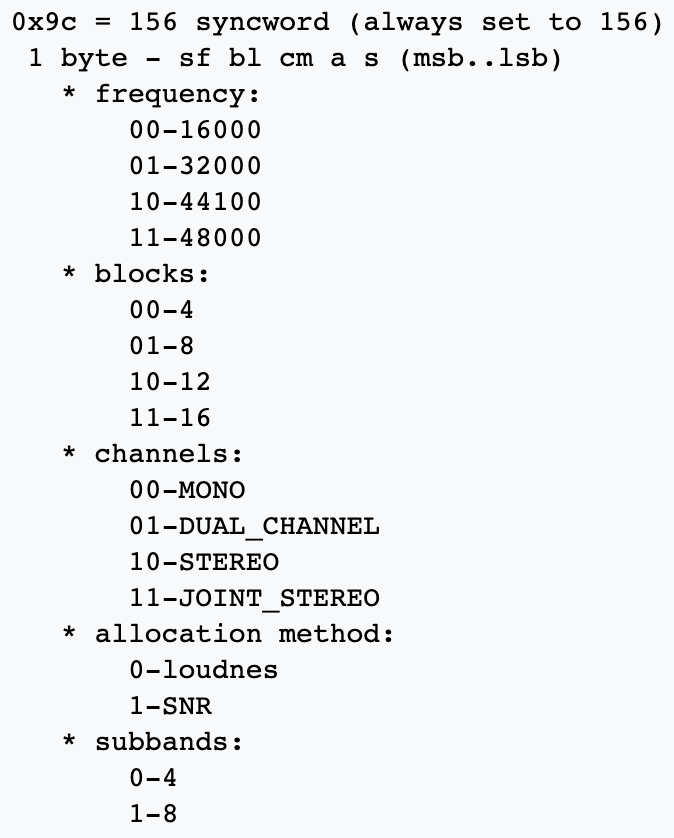
I changed the code a bit to implement the counter too and to test it I downloaded a song from youtube by using an online converter (youtube -> MP3). I converted the MP3 file to an SBC file by using a Gstreamer plugin called SBCENC. GStreamer can be used to build a system that reads files in one format, processes them, and exports them in another. Refer to this page to know more about how to install it.
SBCENC module options available:
audio/x-sbc, rate=(int){ 16000, 32000, 44100, 48000 }, channels=(int)[ 1, 2 ], channel-mode=(string){ mono, dual, stereo, joint }, blocks=(int){ 4, 8, 12, 16 }, subbands=(int){ 4, 8 }, allocation-method=(string){ snr, loudness }, bitpool=(int)[ 2, 64 ]
The command I used to convert the file from MP3 to SBC:
$ gst-launch-1.0 -q filesrc location=audiofilename.mp3 ! decodebin ! audioconvert ! audiosample ! sbcenc ! "audio/x-sbc,rate=32000,channels=2,channel-mode=dual,blocks=16subbands=8,allocation-method=loudness,bitpool=25" ! queque ! filesink location=audiofilename.sbc sync=false
The script I wrote reads the SBC file byte by byte and creates a report with id 15 (334 bytes) every second. Every report is sent to the DS4 via Bluetooth (/dev/hidraw1). I chose the id 15 because I could also set the LED color and spin the vibration motors.
Even if the audio is a bit stuttery I think it does its job very well. The full PoC is available on GitHub. (Sorry for the horrible code).
Redirect the DualShock 4 Bluetooth Signal
In addition, I extended the Bluetooth antenna so I could enjoy some blues from my garden. Chilling on my hammock. With a nice espresso, why not? :)
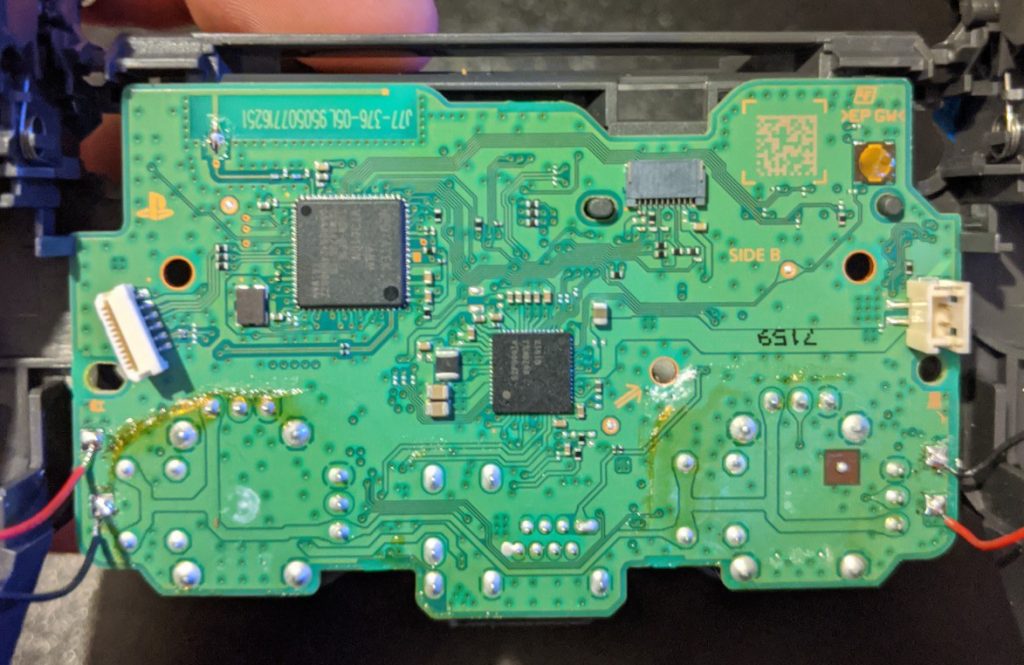
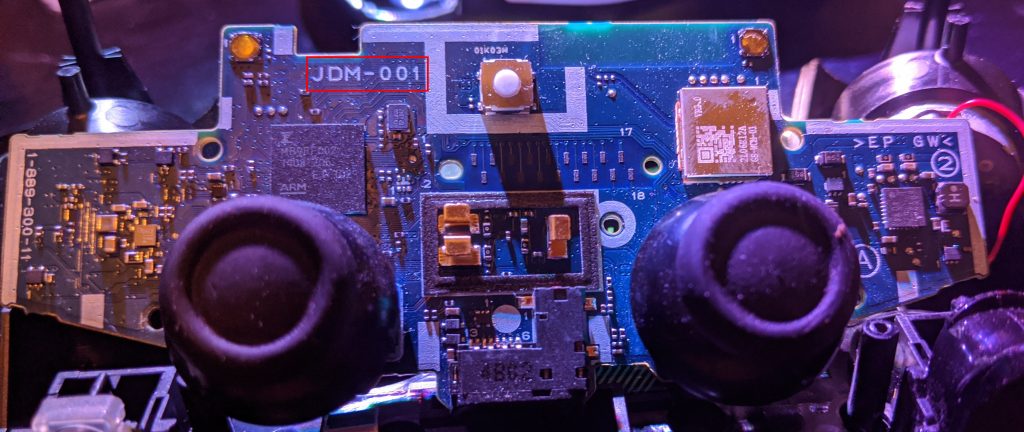
On the JDM-001, JDM-011, and JDM-020, the Bluetooth antenna circuit was more easy to find.
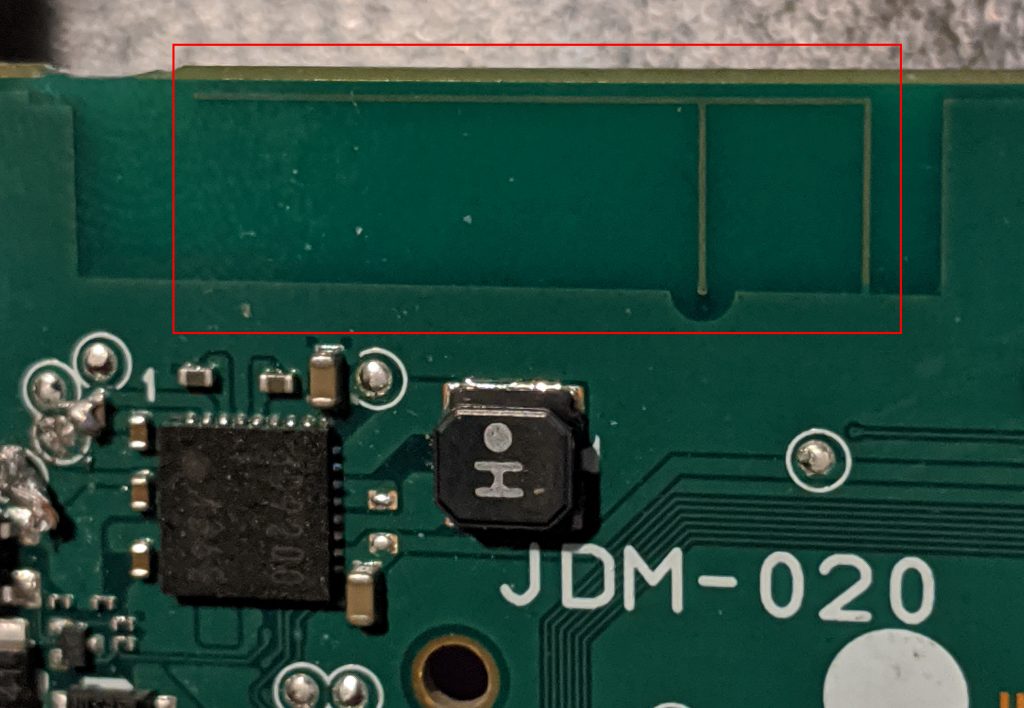
On the B side, there were two pins that could be used to extend the BT antenna. There was the possibility of adding one or two antennas.

The PCB labeled JDM-030, instead, looked like it was equipped with a mini IPX female connector. This means that an antenna extension could be plugged into it.
Below is some information about how to extend the BT antenna on a DS4 v1 (JDM-020).
Requirements
- 1 DS4;
- 1 Indoor Omni-directional antenna (2.4GHz 6dBi);
- 1 Soldering iron;
- Wires.
Here is the antenna I used for this experiment.




Proudly made by one of those lazy Italians.
HAPPY HACKING! <1337
